Information Security Aspects
Assess and monitor confidentiality, integrity, and availability requirements for processes and assets
Assets
Meet all asset management requirements of an ISMS
Controls
DaIM supports evidence management of all essential controls
Awareness
Communicate vulnerabilities and educate employees from onboarding to employee exit
DaIM Information Security – The Protection of Operational Assets is an Entrepreneur’s Duty
The digitization of the world of work offers advantages, but also more scope for attack.
In the future, companies will be required to ensure a minimum level of information security when handling customer-relevant information. DaIM – Information Security implements the specific requirements of ISO 27001. As a result, their entire IT infrastructure will be better protected against sabotage, terrorist acts or other potential threats such as industrial espionage in the future.

Integrated Management Systems
DaIM Information Security contains specific extensions for your Information Security Management System (ISMS) according to ISO 27001 or other implemented Information Security Standards (TISAX, VDA, BSI). All known functions of the high level structure in DaIM are also integrated.
Specific Functions in Information Security Management Systems
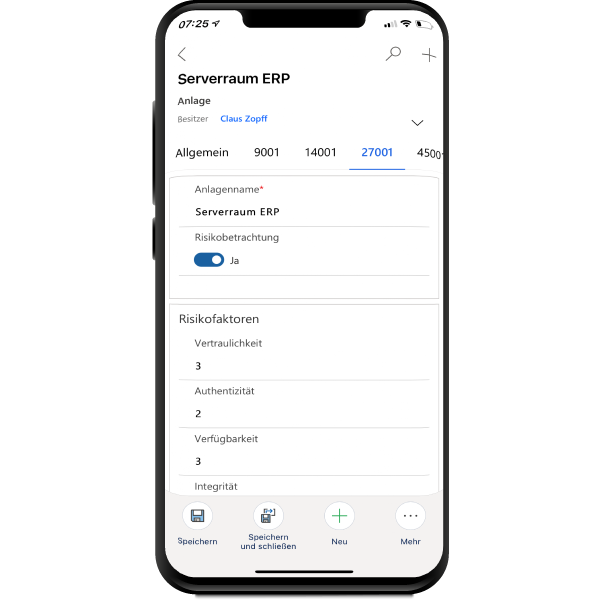
Asset
In asset management, information security assets including mobile device management are inventoried and classified, responsibilities (roles and rights) are regulated, and criticality is classified based on information security aspects.
Risk
Information security risks are created and classified in Risk Management with specific asset reference. Each risk is assigned to the specific controls of ISO 27001. Based on defined acceptance criteria, a risk treatment plan is derived and monitored.
Awareness
Employees are the key to a successful ISMS. Special awareness training courses are planned and implemented in training management. For this, the possibilities of online instructions in Teams., Stream and Forms are used.
Statement of Applicability (SoA)
In the scope, exclusions are defined and the SoA is automatically generated as documented information.
Vulnerabilities
Vulnerabilities are identified from internal and external sources and monitored in Monitoring. For this purpose, the integration possibilities of Microsoft Graph are used. Workflows automate the reporting and recording of vulnerabilities.
Security Zone
Based on the location, the buildings and areas are classified into security zones. The focus is on the assets of the ISMS that require protection. Data protection tours monitor and document compliance with the policies.
Controls
A set of individual policies for administrators and users are provided to employees in the document management system in accordance with the ISO 27001 Annex and distributed via MS Teams.
Security Incident
All information security incidents are recorded and assessed. The reporting chain is automatically triggered and all relevant parties are informed. The upgrading of the incidents is an automatic input parameter for the review. Root cause analysis and action tracking to improve information security is transparently documented.
The core components of DaIM
App
A central app for communication and collaboration in Microsoft Teams. With the data-based implementation of all standard requirements, processing is possible anytime and anywhere.
Documents & Processes
Securely edit documented information and processes efficiently, approve and authorize effectively, and keep them linked to the DaIM App's protected data.
Connector
Efficient handling of existing data by connecting data sources based on hundreds of proven data connectors. Deep insights by integrating all relevant data from the enterprise across all standards.
Review
Real-time management review at the click of a mouse. Minimize the effort for recurring evaluations. Compare the results of your management reviews.
Digital Auditor & AI
AI is not only about certification readiness of your management systems, but also about changing the way your employees work. With the Digital Auditor and the Improvement Engine you transfer your management system approach into the digital age.
Audit Mining
Real-time management review at the click of a mouse. Minimize the effort for recurring evaluations. Compare the results of your management reviews.
Innovative Technologies
The functional fusion of leading collaboration tools makes DaIM unique and the most advanced management system in the world today.
Functions
Asset management
Complex asset management over the entire life cycle
Audit management
Planning, execution and reporting from a single source
Compliance management
Binding obligations and material evidence at a glance
Document management
Collaborative work and database-supported management of electronic documents
Incident management
Intuitive recording and seamless tracking of events
Hazardous materials management
Safe handling of hazardous materials through systematic processes
Maintenance management
Preventing malfunctions through efficient maintenance
Key figure management
Flexible key figure system for monitoring business processes
Context management
Identifying and anticipating the expectations of interested parties
Measures management
Centralized control of corrective and preventive measures from all sources
Means of measurement management
Mapping of means of measurement hierarchies and maintenance of means of measurement capability
Process management
Identification, visualization, documentation, control and optimization of business processes
Resource Management
Organization of competencies, authorities and tasks for management teams
Risk management
Monitoring opportunities and risks in an intelligent way
Training management
Demand-driven training organization and record keeping
Scopemanagement
Clearly define scopes and exclusions through transparent scoping